Improved Biba model based on trusted computing - Liu - 2015 - Security and Communication Networks - Wiley Online Library

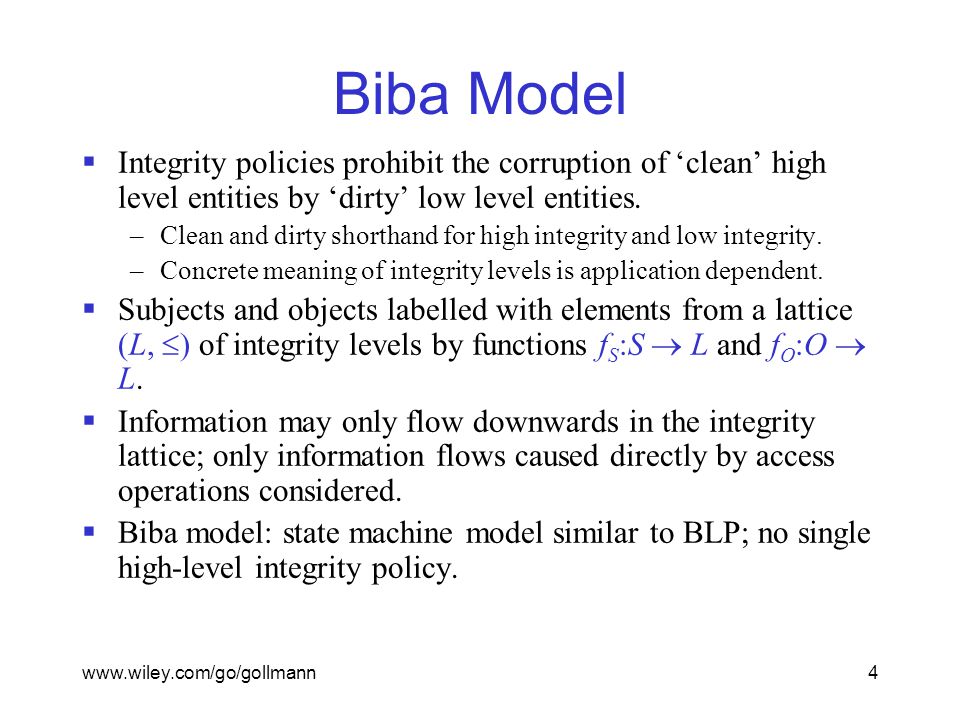
Lecture 2: Security Policy Models Fred Chong CS290N Architectural Support for Secure and Reliable Computing. - ppt download
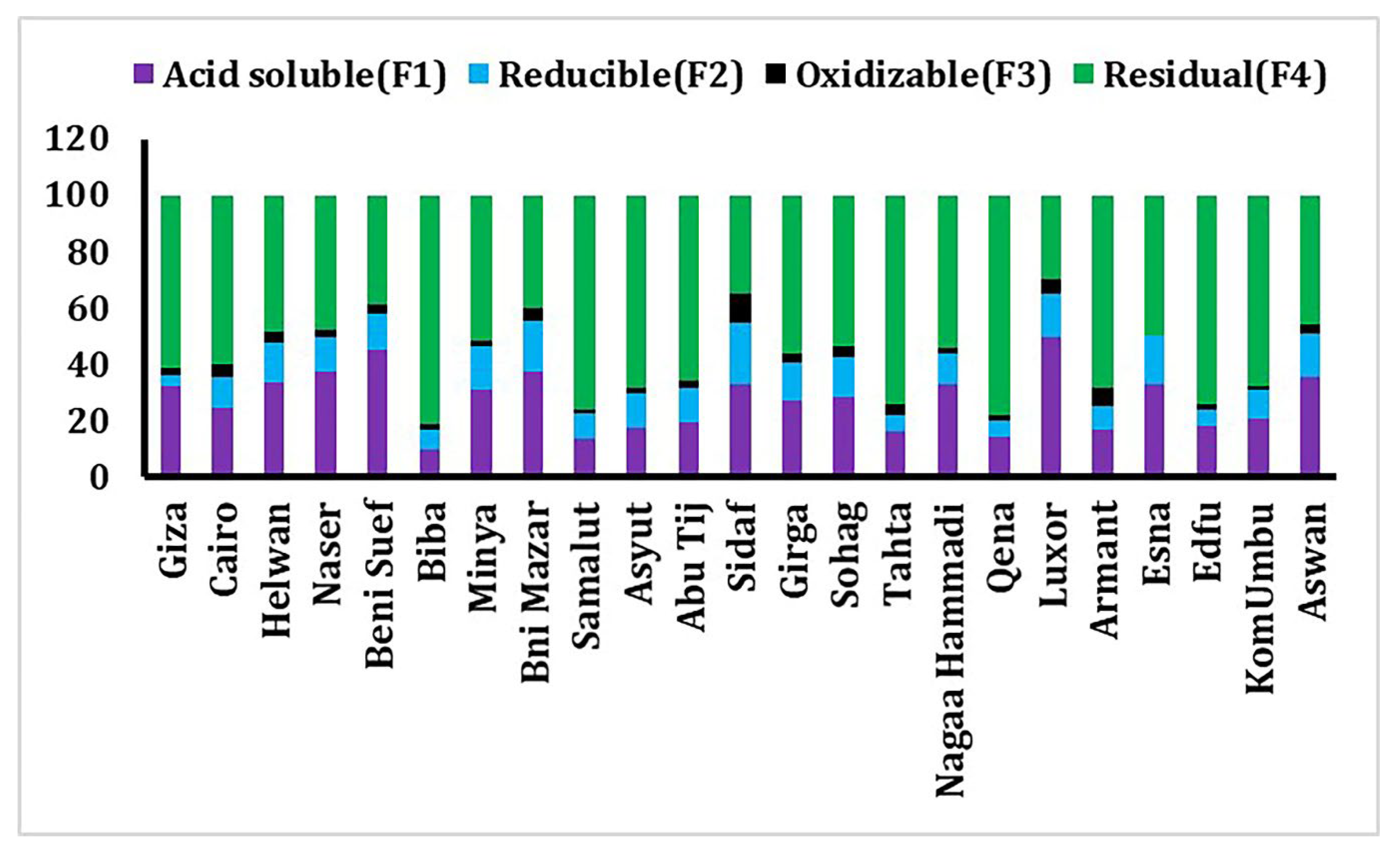
Toxics | Free Full-Text | Environmental Geochemistry and Fractionation of Cadmium Metal in Surficial Bottom Sediments and Water of the Nile River, Egypt